Specifying hacking-resistant access control

Photos courtesy Farpointe Data
The accountability of security professionals
Interestingly, some security professionals do not seem to secure their own equipment. Over the past year, as noted already by the FTC in the D-Link case, users have learned IP-enabled contactless card readers and wireless cameras have become favorite targets of hackers. Unsecured, they provide irresistible back doors. Thus, new specifications are needed for electronic access control projects.
Let us begin by understanding one of the easiest problems to correct with security equipment. Simply putting the default installer code in a disarmed state allows one to view user codes—including the master code—or to change or create a new code. In other words, if an unauthorized person gains access to a panel in the unarmed state, using the installer code can give him or her access to all installed hardware. Any code they create or change then trumps the master and other user codes.
If the installer does not change the default code, he or she might as well be giving a user code to everyone. All it takes to view the master and user codes or create a new one is less than 30 seconds. However, what if the installer says they do not have the default installer code? Unfortunately, these codes can too often be found online by anyone who knows how to conduct a simple Google search. Once ‘inside,’ the hacker can gain access to the rest of the computer system.
Sometimes the problem is within the software itself. Often, the default code is embedded in the app so it can provide a mechanism to let the device be managed even if the administrator’s custom passcode is lost. However, it is poor developer practice to embed passwords into an app’s shipped code, especially unencrypted.
Adding to the problem is the fact Wiegand—the industry-standard over-the-air protocol that is commonly used to communicate contactless credential data to an electronic access reader—is no longer inherently secure. Today, no one would accept usernames and passwords being sent over an unsecured Internet portal, nor should they accept such vulnerable credential data. Anyone with a modicum of hardware hacking skills and a budget of less than $500 can obtain a copy of the master encryption key and create a portable system for reading and cloning Wiegand cards.
ID harvesting has become one of the most lucrative hacking activities. In these attacks, one or more of a credential’s identifiers are cloned or captured, then retransmitted via a small electronic device. For this reason, options can now be added to readers. Some provide a higher-security ‘handshake,’ or code, between the card, tag, and reader to help ensure the reader only accepts information from specially coded credentials. Another relatively new anti-tamper feature can, when embedded, add an additional layer of authentication insurance. Available with contactless smart card readers, cards, and tags, it effectively helps verify the sensitive access control data programmed to a card or tag is indeed genuine and not counterfeit.
Role of the specifier
When considering any security application, it is critical for the specifier to realistically assess the threat of a hack to the facility. For example, if access control is being used merely as a convenient alternative to using physical keys, chances are the end-user has a reduced risk of being hacked. However, if the access system is intended to respond to a perceived or imminent threat generated by the nature of what is done, produced, or housed at the facility, the user may indeed be at higher risk. He or she should consider methods to mitigate the risk of a hack.
The following steps may be considered in reducing the danger of hacking into a Wiegand-based system.
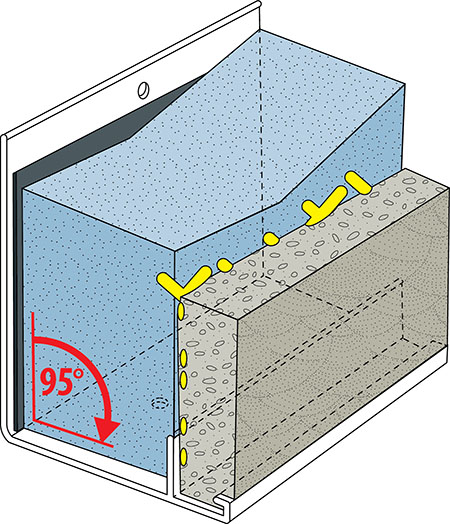
- Install only readers that are fully potted. (‘Potting’ is a hard epoxy seal that does not allow access to the reader’s internal electronics from the unsecured side of the building.) An immediate upgrade is recommended for readers failing to meet this standard.
- Make certain the reader’s mounting screws are always hidden from normal view. It is best to use security screws whenever possible.
- Embed contactless readers inside the wall, not simply on the outside, to effectively hide them from view. If that is not possible and physical tampering remains an issue, consider upgrading the site to incorporate readers providing both ballistic and vandal resistance.
- Use reader cable with a continuous overall foil shield tied to a solid-earth ground in a single location. This helps block signals from being induced onto the individual conductors making up the cable, as well as signals that may be gained from the reader cable.
- Deploy readers with a pigtail (i.e. a cable that has an appropriate connector on one end and loose wires on
the other, designed to patch into an existing line or to terminate the ends of a long run) rather than a connector. Use extended-length pigtails to ensure connections are not made immediately behind the reader. - Run reader cabling through a metal conduit to secure it from the outside world, making certain the conduit is tied to an earth ground.
- Add a tamper feature such as Valid ID.
- Use the ‘card present’ line available on many access control readers. This signal line lets the access control panel know when the reader is transmitting data.
- Provide credentials other than those formatted in the open, industry-standard 26-bit Wiegand. Not only is the 26-bit Wiegand format available for open use, but many of the codes have been duplicated multiple times. Alternatives can include American Banders Association (ABA) Track II, Open Supervised Device Protocol (OSDP), RS-485, and Transmission Control Protocol/Internet Protocol (TCP/IP).
- Offer the customer cards that can be printed and used as photo badges, which are much less likely to be shared.
- Employ a custom format with controls in place to
govern duplication. - Offer a smart card solution employing sophisticated cryptographic security techniques, such as Advanced Encryption Standard (AES) 128-bit.
- Make nontraditional credentials with an anti-playback routine available (e.g. transmitters instead of standard cards and tags). Long-range transmitters offer the additional benefit of not requiring a reader to be installed on the unsecured side of the door. Instead, they can be installed in a secure location such as the security closet—perhaps up to 61 m (200 ft) away.
- Provide two-factor readers including contactless and PIN technologies. It is suggested users change PINs on a regular basis. If required, it is best to offer a third factor—normally, a biometric technology (e.g. face, fingerprint, voice, vein, or hand).
Professionals should ensure additional security system components are available. Such systems can play a significant role in reducing the likelihood of an attack, as well as mitigating the impact of a hack attack should it occur. For example, should the access control system be hacked and grant entry to an unauthorized individual, a burglar alarm or video system can detect, record, and annunciate the intrusion. It is also helpful to ensure any guards in the control room—as well as those performing a regular tour—receive an alert notifying them someone has physically tampered with the access control system. With the proper tools, any of these assaults can be defended against.